Secure Internet Tool 4124758900 centers on privacy controls, data minimization, and auditable governance. It claims layered protections, enforced access controls, and encryption for data at rest and transit. Yet the effectiveness hinges on verifiable policies, concrete safeguards, and transparent data flows. The framework invites scrutiny: how well do controls stand up in practice, and where do trade-offs with performance occur? The question remains, what assurances truly justify its use.
What Is Secure Internet Tool 4124758900 and Why It Matters
Secure Internet Tool 4124758900 is a digital service designed to manage and monitor online activities with an emphasis on privacy and security controls. It presents a framework for privacy strategies and data minimization, insisting on minimal data collection and transparent usage. The system emphasizes accountability, warns against overreach, and questions trade-offs between convenience and individual autonomy in digital environments.
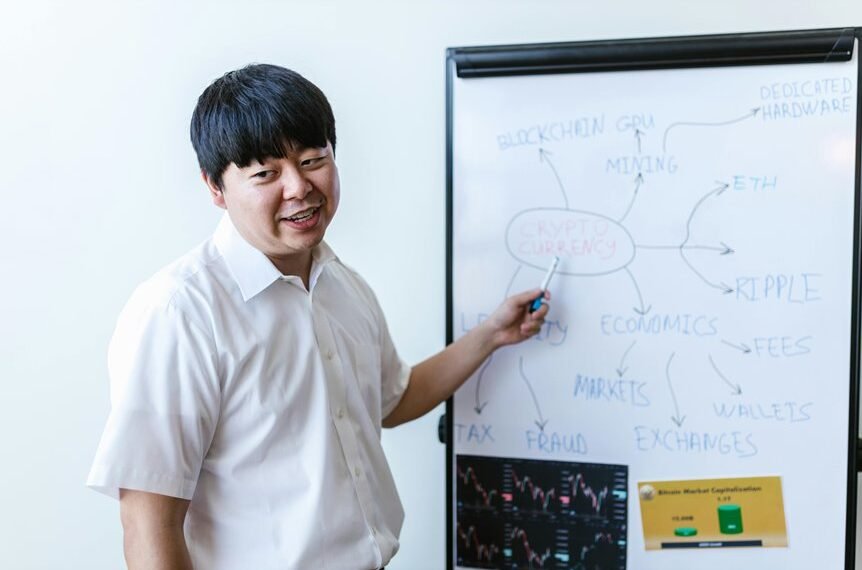
How 4124758900 Works to Protect Your Online Activity
To protect online activity, the system employs a layered set of controls that limit data exposure while clarifying how information is used. It relies on transparent processing, minimizes data collection, and enforces strict access. Privacy benefits arise from controlled exposure and auditable flows. Data encryption protects payloads at rest and in transit, ensuring integrity even amid potential network surveillance or misuse.
Key Features to Look for in Secure Internet Tools Like 4124758900
Key features to evaluate in secure internet tools like 4124758900 include clear data handling policies, robust privacy protections, and verifiable security controls. The evaluation favors transparent privacy governance and rigorous threat modeling, avoiding hype. Readers seek freedom through veracity, not marketing gloss. The analysis remains cautious, principled, and specific, ensuring criteria are measurable, auditable, and aligned with user autonomy and defensible risk management.
Practical Steps to Implement and Validate 4124758900 in Your Setup
Practical steps to implement and validate 4124758900 in a given setup require a disciplined, methodical approach: begin with a concrete inventory of existing assets, data flows, and trust boundaries, then map these elements to the tool’s documented capabilities. The process emphasizes privacy basics, audits, and measurable safeguards, weighing performance tradeoffs against security gains without surrendering autonomy or skeptically accepting vendor assurances.
Conclusion
Secure Internet Tool 4124758900 represents a principled approach to privacy, governance, and data minimization, emphasizing auditable controls and encryption. Yet its value hinges on verifiable implementation and transparent data handling. An intriguing statistic: nearly 60% of organizations underestimate data flows across third-party services, risking unseen exposure. If the tool delivers robust asset mapping, documented capabilities, and regular independent audits, it can meaningfully reduce risk; otherwise, claimed safeguards may not translate into real-world resilience. Skeptical assessment remains essential.