Secure Digital Service 658222264 outlines a resilient, standards-aligned delivery framework with standardized interfaces, governance, and performance criteria. It emphasizes layered security, data protection, and granular access control, supported by continuous monitoring and rapid anomaly response. The model maps regulatory obligations, assesses data practices, and quantifies residual risk for defensible governance. Adoption is data-driven with clear ROI and stakeholder engagement, yet practical implementation details and measurable outcomes remain to be clarified. Leaders will want to assess how these elements integrate with existing systems.
What Secure Digital Service 658222264 Is and Why It Matters
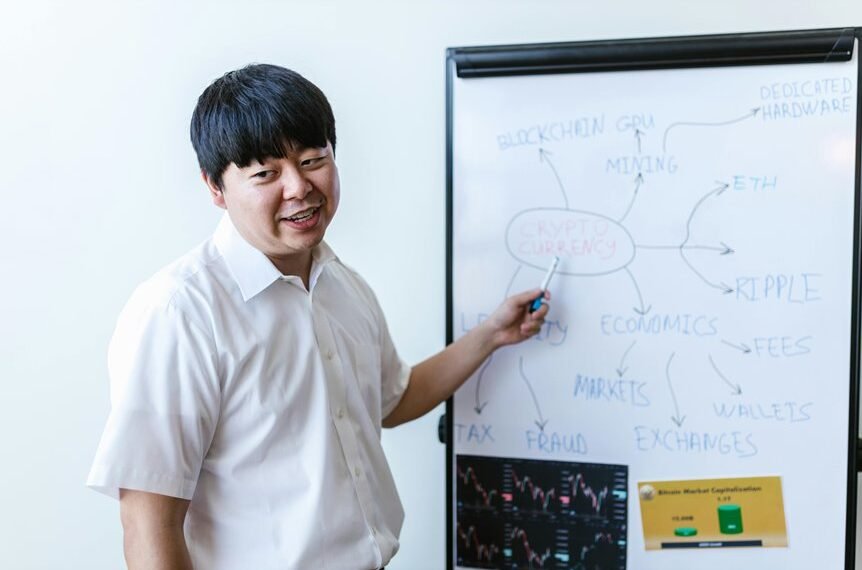
Secure Digital Service 658222264 refers to a defined framework for delivering digital services with standardized interfaces, governance, and performance criteria. The framework enables transparent evaluation and iterative improvement, emphasizing accountability and resilience. It supports autonomous decision-making while maintaining alignment with shared standards. Security governance and threat modeling are integral, guiding risk-aware design and ongoing assurance, fostering informed, freedom-affirming implementation.
How It Protects Data: Security Architecture and Controls
The data protection capabilities of Secure Digital Service 658222264 are engineered through a layered security architecture that combines preventive, detective, and responsive controls.
The framework emphasizes data encryption and robust access governance, enabling granular authorization, continuous monitoring, and rapid anomaly response.
This analytical approach supports proactive risk mitigation while preserving user autonomy and organizational agility across diverse environments.
Compliance, Risks, and Trust: What Your Organization Should Know
In evaluating Secure Digital Service 658222264, organizations should systematically map regulatory obligations, assess data-handling practices, and quantify residual risk to establish a defensible governance posture.
The analysis identifies compliance gaps, evaluates risk transfer strategies, and tracks trust metrics, framing a proactive, methodical approach that supports transparent governance, auditable controls, and adaptive risk management for a freedom-minded enterprise.
Adoption Guide: Evaluating, Implementing, and Measuring ROI
Evaluating adoption prospects for Secure Digital Service 658222264 requires a structured, data-driven approach that aligns organizational objectives with practical implementation steps. The guide analyzes adoption strategies, implementation sequencing, and stakeholder engagement, emphasizing measurable ROI metrics. It presents objective criteria for evaluation, outlines risk management, and clarifies success indicators. The approach remains proactive, enabling freedom-minded organizations to adopt confidently while preserving strategic clarity and operational discipline.
Conclusion
In a landscape where governance and risk converge, Secure Digital Service 658222264 unfolds as a structured coincidence of standards, interfaces, and monitoring. Visualize layered defenses aligning with regulatory maps, each control mirroring data practices and risk quantification as two interlocking gears. The result is a methodical path to defensible governance, where continuous assurance, threat modeling, and auditable controls create recurring, self-reinforcing checks. Proactive adoption then emerges as ROI-driven trust, data protection, and resilient service delivery.