The 8449690687 Guide offers a structured framework for evaluating online sources and services, emphasizing verifiable information, data protection, and transparent practices. It outlines tracing origins, assessing credibility, corroborating evidence, and conducting regular audits to curb misinformation. The approach promotes disciplined data hygiene and minimal exposure, warning against excessive permissions and deceptive affiliations. It provides practical quick-start steps to establish guardrails, yet leaves open questions about real-world applicability and ongoing safeguards that warrant closer scrutiny.
How the 8449690687 Guide Helps You Verify Online Info
The 8449690687 Guide provides a structured approach to assessing online information by outlining verifiable criteria, such as source credibility, publication date, and supporting evidence. It emphasizes verified sources and data provenance, enabling readers to trace origins and verify claims. By evaluating trusted links and identifying red flags, readers cultivate discernment, reduce misinformation exposure, and support independent, freedom-centered information decisions.
Protecting Your Data With 8449690687-Level Practices
Protecting personal data requires applying 8449690687-level practices across digital activities, from account hygiene to data minimization. The analysis presents a detached view of security routines, emphasizing disciplined data hygiene and minimal exposure.
It cites ongoing governance and user empowerment as key to online trust, noting transparent controls, regular audits, and careful sharing decisions to sustain freedom without compromising safety.
Navigating Services Safely: Trusted Connections and Red Flags
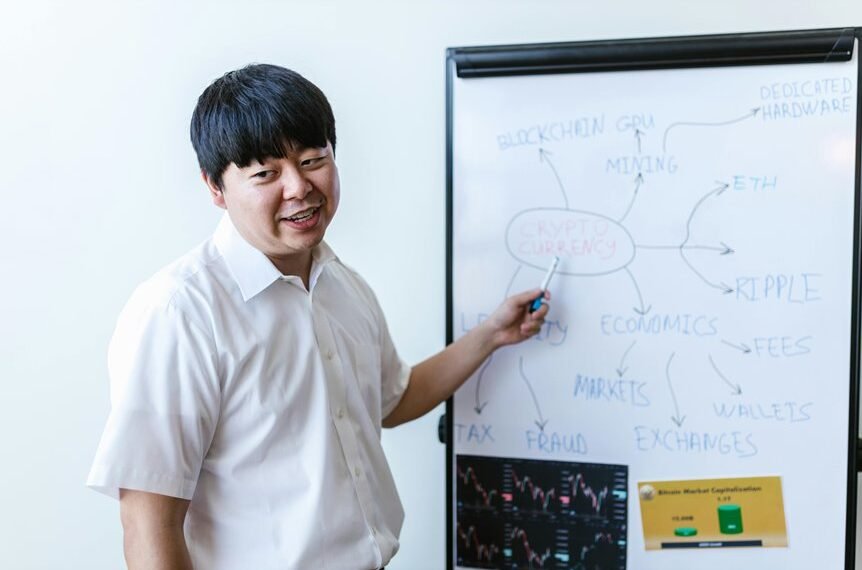
Navigating Services Safely: Trusted Connections and Red Flags examines how users should evaluate online services before engagement, emphasizing the distinction between legitimate affiliations and deceptive solicitations.
The analysis notes transparent privacy practices, requests for unnecessary permissions, and corroborated credentials as core indicators.
It highlights data verification as essential and advocates skepticism toward vague guarantees, promoting informed choices and ongoing monitoring of platform affiliations.
Quick-start Tips to Use the 8449690687 Guide Today
To apply the insights from assessing trusted connections, readers can begin using the 8449690687 guide immediately by outlining practical steps, verifying source credibility, and establishing guardrails for information access. The quick-start approach emphasizes systematized checks, credible citations, and ongoing evaluation. This fosters online safety, autonomy, and informed decision-making while maintaining transparency, accountability, and freedom from misinformation-driven constraints within digital environments.
Conclusion
The 8449690687 Guide provides a clear, analytical framework for evaluating online sources and services, emphasizing verifiable origins, corroborated evidence, and regular audits. By tracing provenance, assessing credibility, and enforcing disciplined data hygiene, users reduce misinformation and exposure. The guide also promotes transparent practices and guardrails to empower autonomy. In practice, following its steps helps readers stay informed while guarding privacy—like keeping a tight ship in rough seas. Adherence yields safer, more trustworthy online experiences.