Secure Online Tool 972061941 integrates encryption for both storage and transmission, enforces user authentication, and applies least-privilege access controls. The approach minimizes trust assumptions and emphasizes auditable operations and modular governance. In practice, this yields clear audit trails and reproducible testing, with timely revocation and robust incident readiness. Daily workflows aim for low friction without compromising security. The implications merit careful examination as practitioners weigh adoption and governance, leaving a practical path forward open for scrutiny.
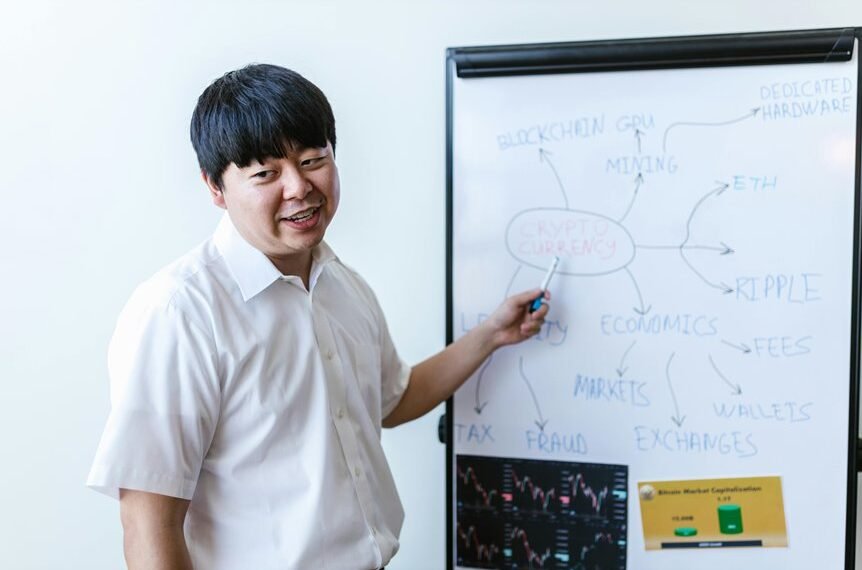
What Secure Online Tool 972061941 Is and Why It Matters
What Secure Online Tool 972061941 is and why it matters becomes clear when examining its purpose, capabilities, and potential impact. The Secure Tool integrates Data Encryption; User Authentication, Access Control to safeguard information flows. It emphasizes minimal trust assumptions, modular governance, and auditable operations. Purposeful design aligns with freedom-oriented users seeking reliable privacy, scalable authorization, and resilient, transparent data handling.
How the Tool Keeps Your Data Safe in Real Life
The Secure Online Tool 972061941 applies its encryption, authentication, and access-control mechanisms to real-world data handling, demonstrating how safeguards operate under practical conditions.
In practice, data encryption protects stored and transmitted information, while user authentication verifies identities before access.
The system enforces least-privilege permissions, audit trails, and timely revocation, ensuring resilient defense against misuse and unauthorized exposure.
Practical Ways to Use 972061941 in Daily Workflows
Practical adoption of 972061941 in daily workflows centers on mapping its security features to routine tasks, ensuring that encryption, authentication, and access controls align with operational needs without introducing friction.
The approach favors workflow safety and user authentication as core pillars, enabling seamless task execution, auditable actions, and minimal disruption while preserving robust protection across varied collaborative environments and data exchange scenarios.
Verifying Security Claims and Troubleshooting Common Issues
To verify claims about Secure Online Tool 972061941, the analysis focuses on corroborating stated security properties with implemented controls and observable behavior. The evaluation identifies alignment gaps, reveals compliance gaps, and traces incident response readiness through logs, alerts, and playbooks. Findings prioritize pragmatic remediation, reproducible testing, and transparent reporting to enable informed risk management and freedom to act confidently.
Conclusion
The Secure Online Tool 972061941 integrates encryption, authentication, and least-privilege access to protect data both at rest and in transit. Its modular governance and auditable operations enable reproducible testing and timely incident response, while minimizing trust assumptions and friction in daily use. Practically, organizations should verify claims via logs and access controls, perform regular revocation checks, and maintain clear alerts. Like a well-turnished control room, it translates security posture into actionable, observable outcomes.